What is cryptography ?
Cryptography is the study of securing communications from those for who intend to read and possibly misuse the sensitive content of the communication.
Encryption algorithms are used to encrypt the data by taking the original message, or plaintext, and converts it into cipher-text, which is not understandable.
There are five primary functions of cryptography:
- Privacy/confidentiality: Making sure that no one can read the message except the intended receiver.
- Authentication: The process of proving one’s identity.
- Integrity: Assuring the receiver that the received message has not been altered in any way from the original.
- Non-repudiation: A mechanism to prove that the sender really sent this message.
- Key exchange: The method by which crypto keys are shared between sender and receiver.
Three types of cryptographic techniques used in general.
- Symmetric-key Cryptography: Both the sender and receiver share a single key. The sender uses this key to encrypt plaintext and send the cipher text to the receiver. On the other side the receiver applies the same key to decrypt the message and recover the plain text.
- Public-Key Cryptography: This is the most revolutionary concept in the last 300-400 years. In Public-Key Cryptography two related keys (public and private key) are used. Public key may be freely distributed, while its paired private key, remains a secret. The public key is used for encryption and for decryption private key is used.
- Hash Functions: No key is used in this algorithm. A fixed-length hash value is computed as per the plain text that makes it impossible for the contents of the plain text to be recovered. Hash functions are also used by many operating systems to encrypt passwords.
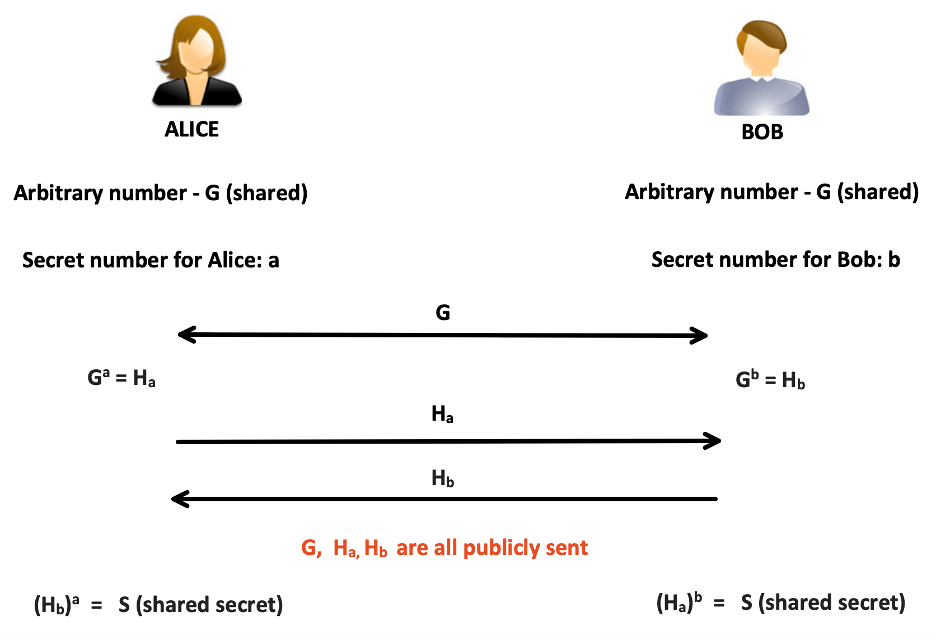
Generic Shared Secret Key
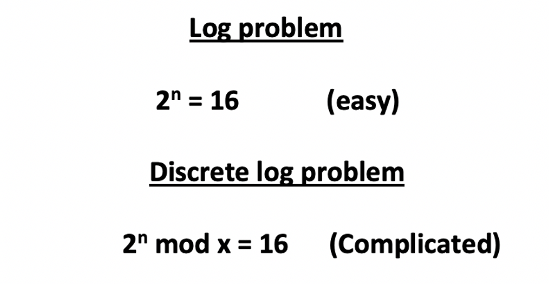
How is Diffie Hellman different? – Its uses “DISCRETE LOG PROBLEM”
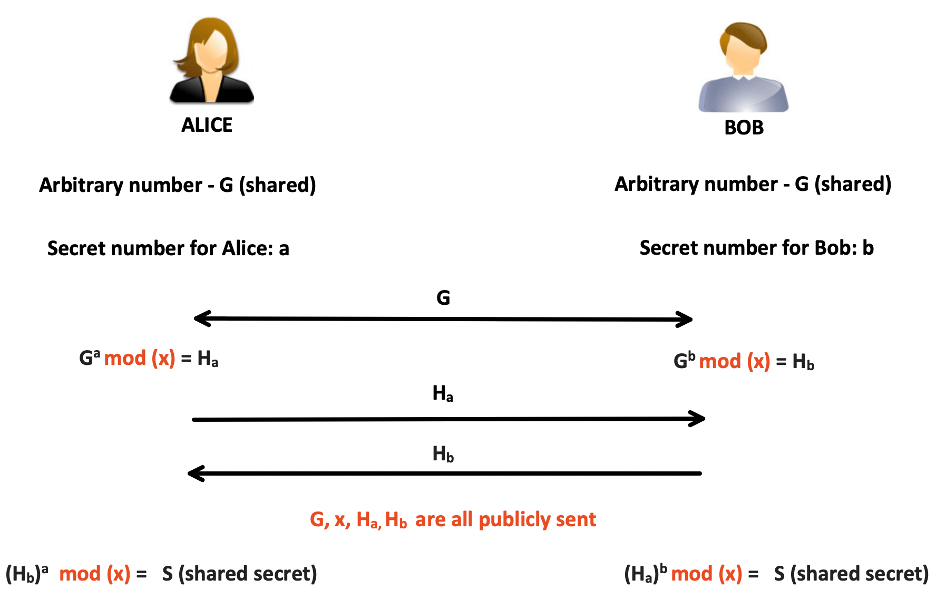
Diffie Hellman Key Exchange:
If Diffie Hellman is so effective, why are we looking for a better solution?
2 main reasons:
- Need of larger key size: With the advancements of algorithm every day, the chances of figuring out discrete log is getting easier. So, we need larger key size to keep it complicated.
- Increased Computation: With larger key size comes high CPU and memory requirement.
What combined with Diffie Hellman could give us smaller key size and reduced computation?
Answer: Elliptic Curve Cryptography

Elliptic curve cryptography
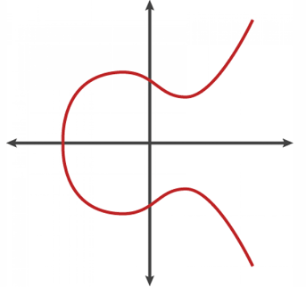
What is Elliptic Curve Cryptography? How is different than Diffie Hellman?
Elliptic curve cryptography (ECC) uses the mathematical properties of elliptic curves to produce public key cryptographic systems.
Like all public-key cryptography, ECC is based on mathematical functions that are simple to compute in one direction, but very difficult to reverse.
X —–> Y (Easy)
Y —–> X (Very difficult)
SOME INTERESTING DETAILS:
There is a point generator in the elliptic curve. If the generated point (x, y) is not a valid point on the elliptic curve, the counter is increased by one and the algorithm is computed again until a valid point has been found.
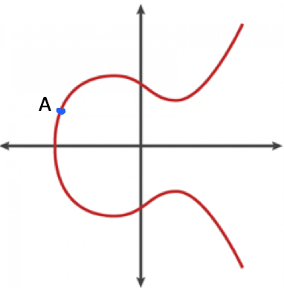
From that point, a line intersects the curve in atmost one other place. From the point of intersection, due to the symmetric behavior of the curve, drop or flip the intersection point to the other half (dimension) of the curve.
This new point can be called 2A or B (2 times A).
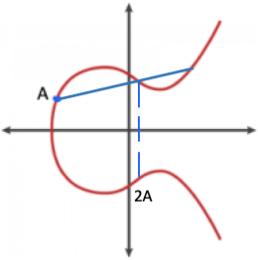
Then considering a finite line between points A and 2A on the elliptic curve, mark the point of intersection and flip back to the initial dimension of the curve and
we can call that as point 3A or C.
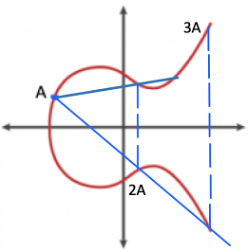
Using the same concept, by forming a line from point 3A to point A, and drop a line from the point of intersection to the other part of the curve and
let’s can call that as 4A or D.
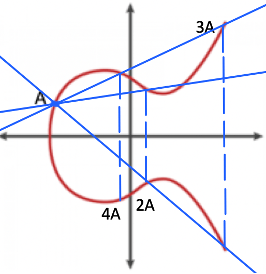
And this keeps going on, so the idea here is these point on curves keep adding up to itself, or we can say this as the concept of “point addition”.
Now, in the same diagram above, if I ask you which point is “?A”, it would be very difficult to figure that out, so that unknown point on the curve is the private number and that’s the number we can’t reverse engineer (atleast easily), cause we don’t really know many points it passed on to give us that private number.

So, if we call this unknown point as E, our equation will be,
Elliptic Curve Discrete Log Problem
nA = E
where nA is A dot A dot A … n times
How DH (Diffie Hellman) and EC (Elliptic Curve) work together?
The ECDH (Elliptic Curve Diffie–Hellman Key Exchange) is anonymous key agreement scheme, which allows two parties, each having an elliptic-curve public–private key pair, to establish a shared secret over an insecure channel.
ECDH is very similar to the classical DHKE (Diffie–Hellman Key Exchange) algorithm, but it uses ECC point multiplication instead of modular exponentiations.
A diagrammatic representation of how would the key exchange would look like

The functions which DH and EC use, works in similar ways, So, if we replace the DH functions with EC this is what it would look like,


References :