IEEE 802.11r was published in 2008 and was aiming for faster and secure handoff’s within the service set. It is also known as Fast Basic Service Set Transition (Fast BSS Set Transition)
Key items involved when we talk about FT,
- Mobility Domain : Mobility Domain (MD) is a set of basic service sets (BSS) with in same Extended Service Set (ESS), which supports Fast BSS Transition between themselves.
Basically, a group of AP’s belonging to the same ESS where client station is expected to roam in a fast and a secure manner.
2. Mobility domain information element (MDIE) – The AP uses the MDIE to advertise that it is included in the group of APs that constitute a mobility domain, to advertise its support for FT capability, and to advertise its FT policy information.
3. Fast BSS transition information element (FTIE) – The FTIE includes information needed to perform the FT authentication sequence during a fast BSS transition in an RSN.
Overview of Key Hierarchy –
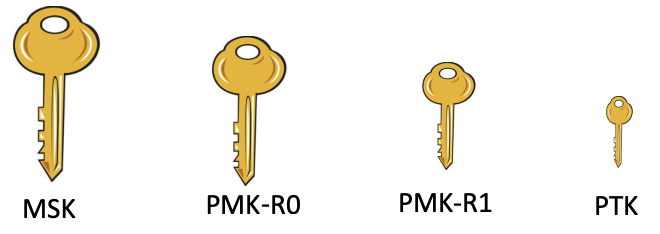
Types of Keys:
- Master Session Key (MSK) : This is the key generated during the EAP transactions (while doing 802.1x) or passphrase (in case of pre-shared based network)
- Pairwise Master Key R0 (PMK-R0) : This key is derived from MSK – First level key of FT key hierarchy.
- Pairwise Master Key R1 (PMK-R1) : This key is derived from PMK-R0 – Second level key of FT key hierarchy
- Pairwise Transient Key (PTK) : Third and final key in the FT key hierarchy created from the PMK-R1 during the 4-way exchange and used to encrypt 802.11 data frames.
Key Holder Role :
| Device | Key Holder Role |
| WLAN Controller | PMK-R0 Key Holder (R0KH) |
| Access Point | PMK-R1 Key Holder (R1KH) |
| Client Station | PMK-S0 Key Holder (S0KH) |
| Client Station | PMK-S1 Key Holder (S1KH) |
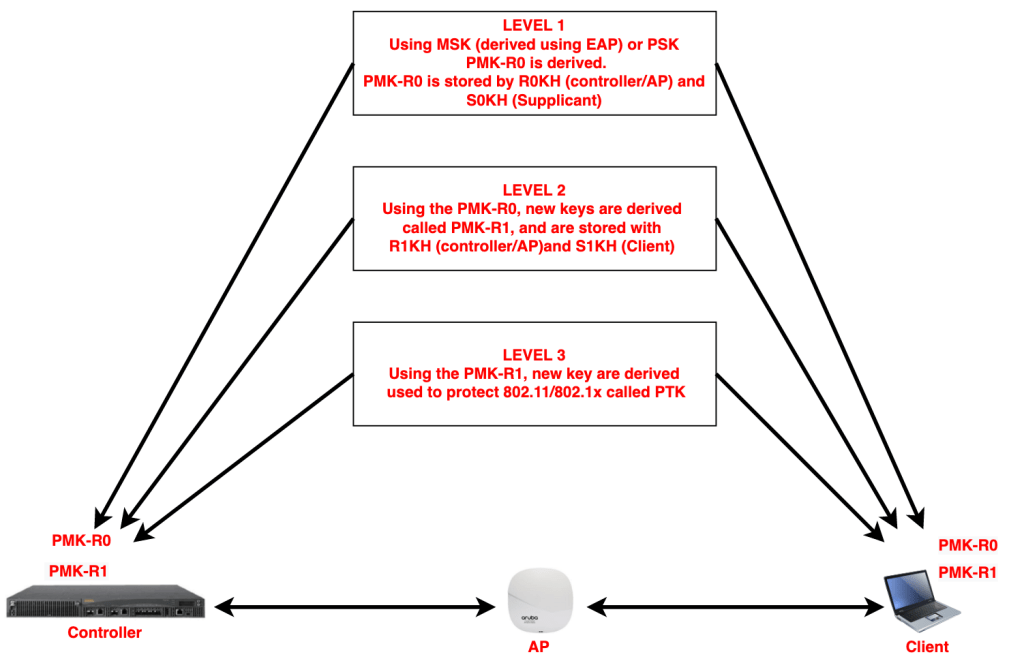
With the generation of MSK (after dot1x completion) or PSK, the Controller (R0KH) and supplicant (S0KH) generates the PMK-R0.
Then R0KH and S0KH with the help of PMK-R0, derives PMK-R1, and are delivered within the same mobility domain to R1KH (controller) and S1KH (Supplicant)
PMK-R1’s are then used to derive PTK’s which are used for protect 802.11 data frames.
Fast BSS Transition Mechanisms :
There are two ways, 802.11R does pre-auth and resource verification before roaming.
- Over-the-Air – This is done over the Air.
Here client changes its channel to the target AP and sends 802.11 auth frame with the Authentication Algorithm set to Fast BSS Transition. - Over-the-DS – This is done over the DS.
Here client sends Fast BSS Transition action frame to existing connected AP destined to the target AP. So the client remains in same channel and connected to existing AP.
Let’s explore these mechanisms using some mgmt frame flow diagrams and packet captures.
NOTE- Aruba wireless controllers and Access Points only supports Over-The-Air mechanism, so I only have the packet captures for this mechanism and not for Over-The-DS.
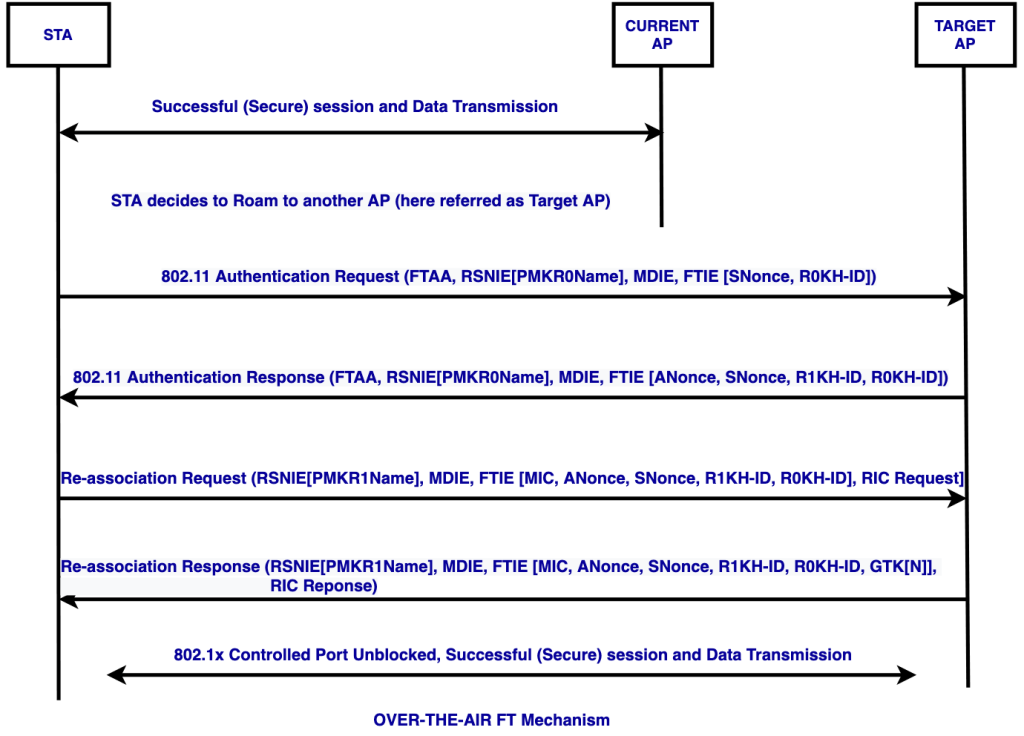
Over-the-Air FT Mechanism –
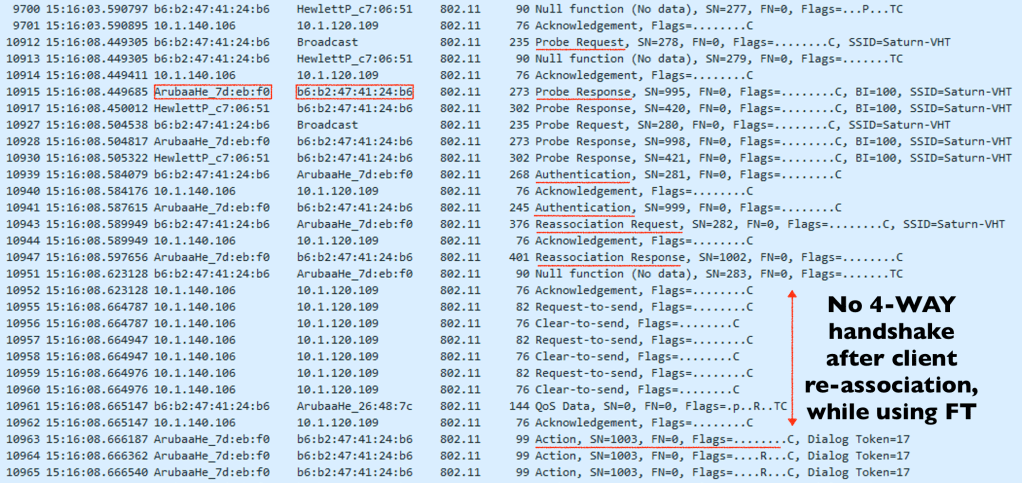
Here is the station and AP communication, where 802.11r is enabled and it roams from one AP to the other.
When using Over-The-Air FT mechanism, the client while deciding to roam to a new AP, will directly communicate to the Target AP and using the authentication and re-association frames (instead of 4-way key exchange) to generate PTK and GTK keys to protect the 802.11 data frames
Beacon Frame:
The Beacon frame which AP keeps broadcasting every second (default), defines the capabilities of that particular SSID and what it can support.
After enabling 802.11r, the AKM suite under the RSN Capabilities field will exhibit the AP/controllers’ ability to use Fast BSS Transition.
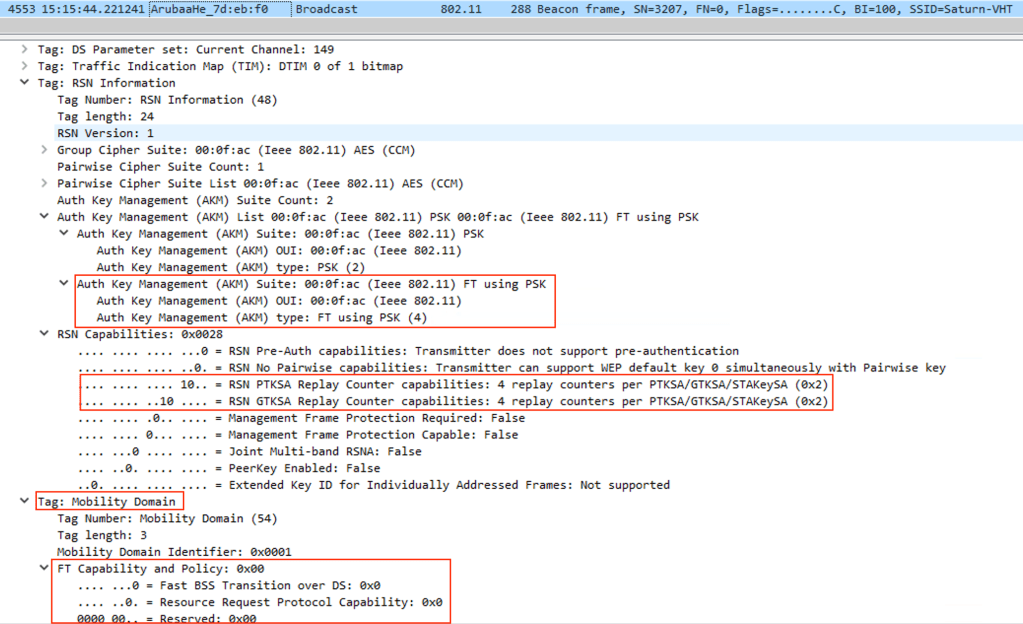
AP 1 BSSID – 00:4e:35:c7:06:51
AP 2 BSSID – 1c:28:af:7d:eb:f0
Client MAC – b6:b2:47:41:24:b6
Before running the below tests, I enabled 802.1r on Aruba Controller and took captures while AP’s were operating on channel 149E
Below screenshot shows initial communication, when the client connects to an 802.11r enabled SSID, for the first time, we can see after the association response there will 4 way key exchange to generate PTK and GTK to encrypt the data frames.
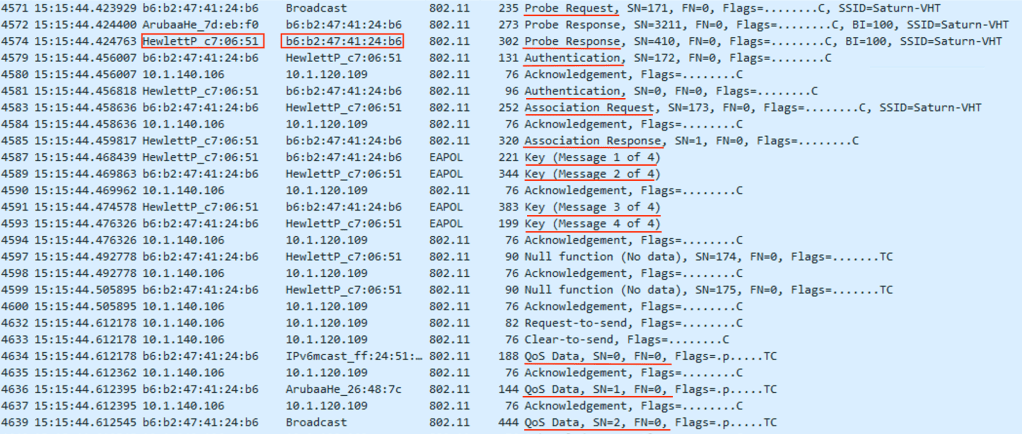
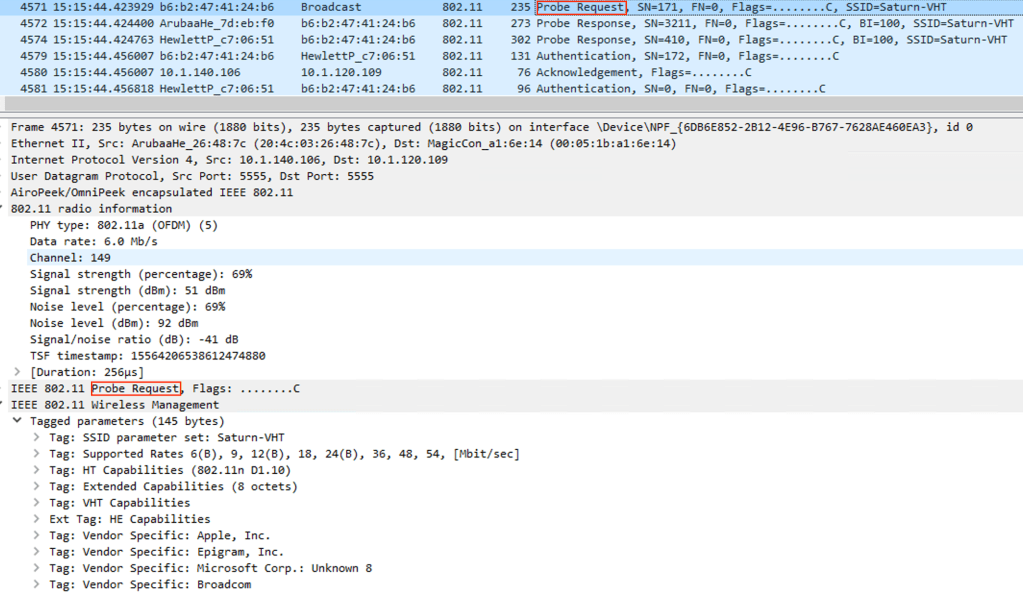
Probe Request :
This is the first broadcast packet sent by the client to connect to an SSID, which ends up reaching to all the AP’s in clients vicinity.
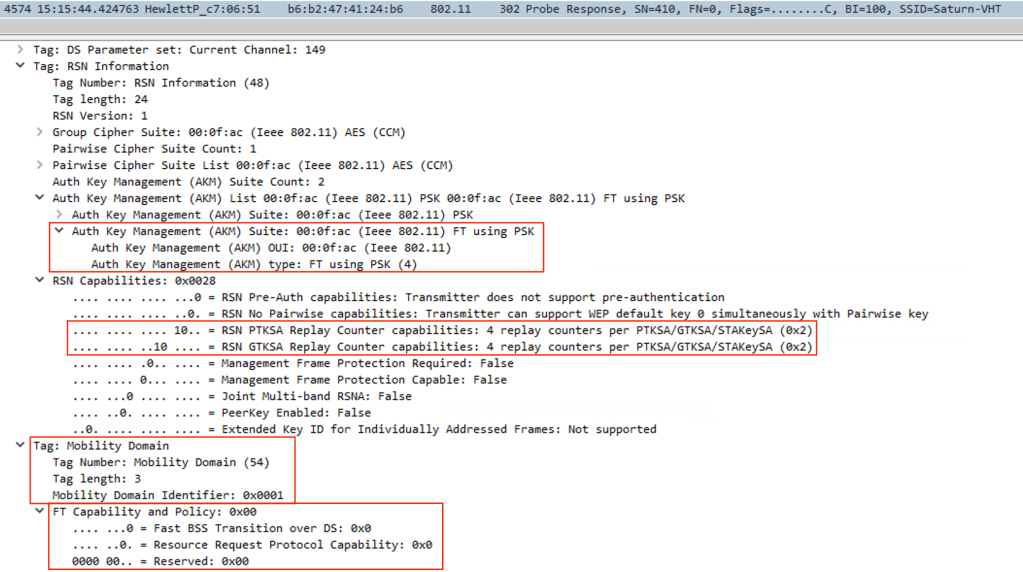
Probe Response :
AP will unicast a probe response with its FT capability support
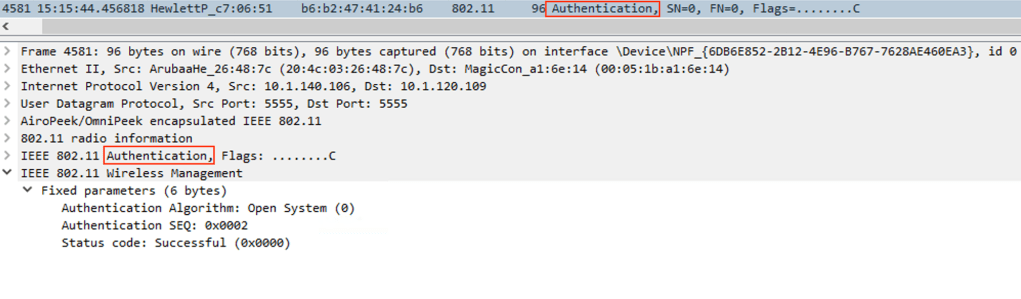
Authentication Sequence :
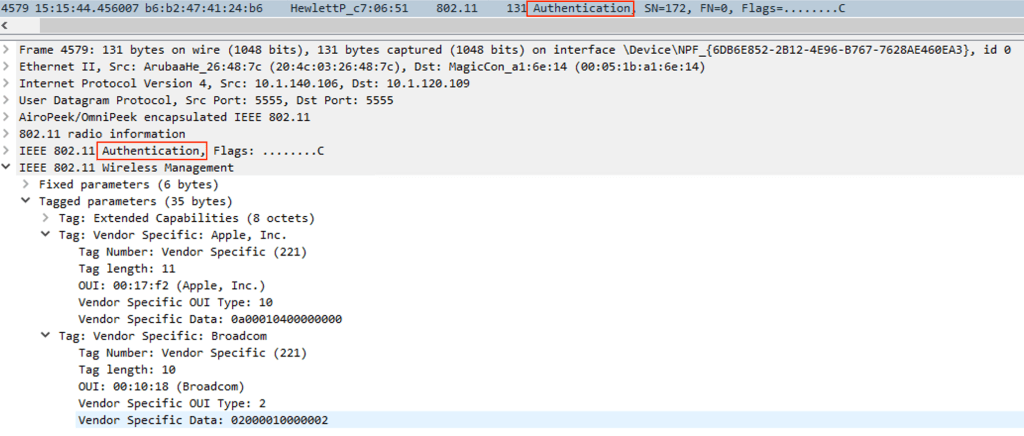
Authentication Sequence
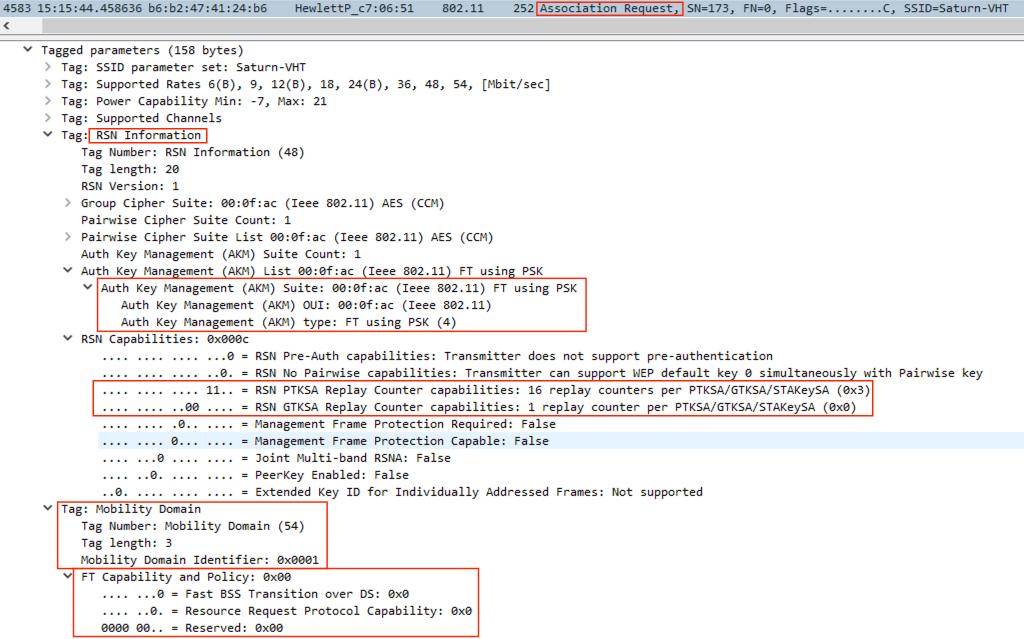
Association Request
Now, client sends its ability to support Fast Roaming.
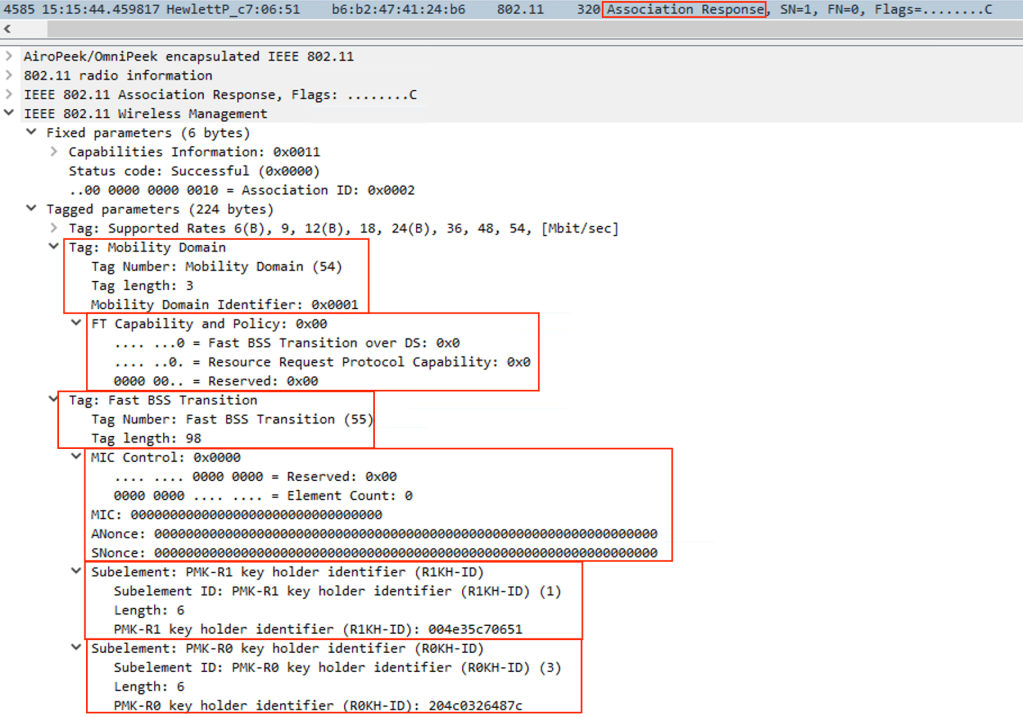
Association Response
In the association response, we can see that the all the MIC control fields are 0, because PTK and GTK will be generated after the regular 4-WAY handshake, since this is initial connection and not yet roamed.
Now the Client roamed from the AP1 to AP2.
How does 802.11r makes roaming much faster?
When 802.11r is not used, on every roam client and AP will perform 802.11i key exchange to generate PTK and GTK, which is additional 4-way communication.
With the use of 802.11r, the PTK and GTK are generated in the Authentication and Re-association frames itself, so no need to re-do the 4-Way key exchange every time, which in turn makes it much faster.
SKIPPING SNIPPETS FOR PROBE REQUEST AND PROBE RESPONSE
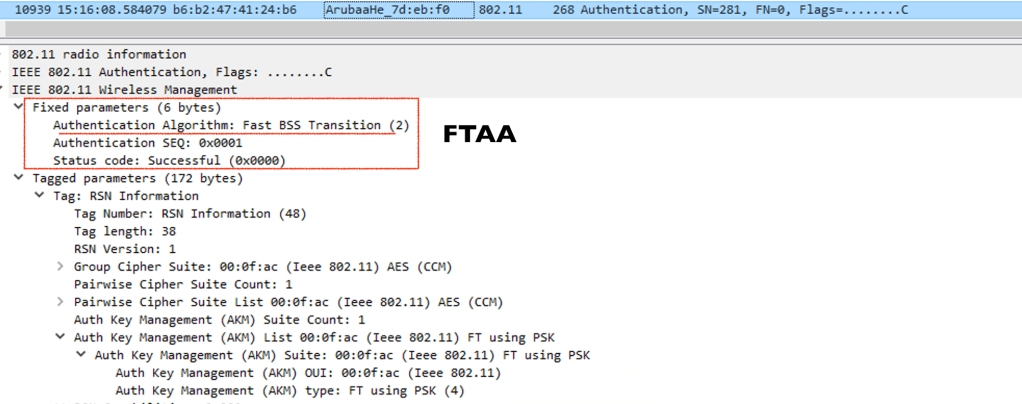
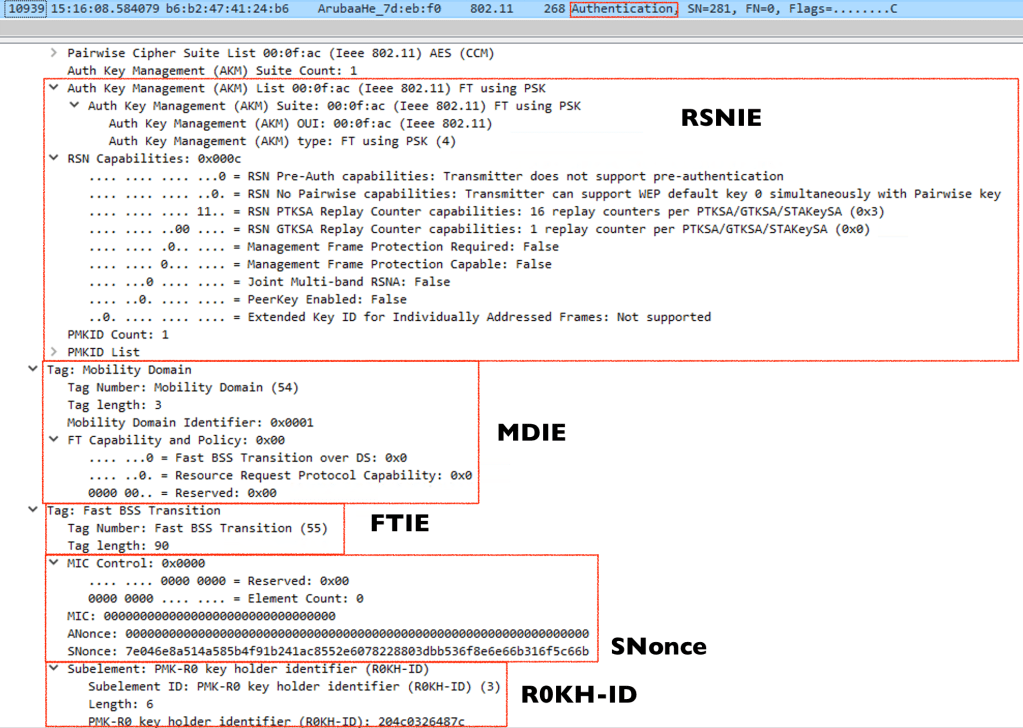
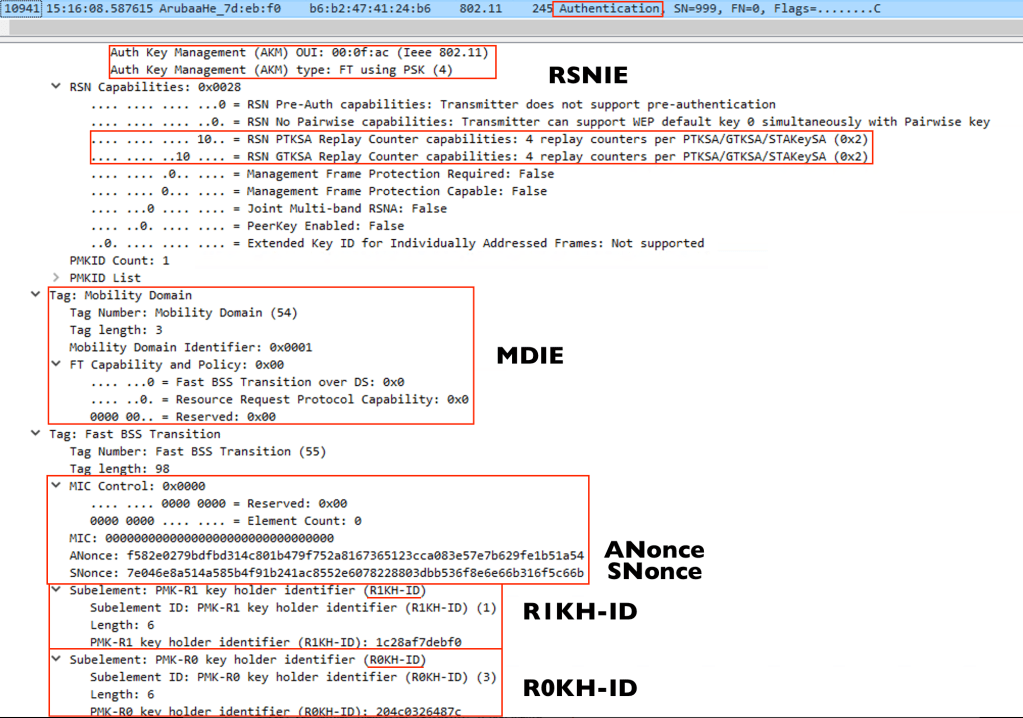
Authentication Sequence 1 –
FTAA – Fast BSS transition authentication algorithm
RSNIE – Robust Security Network information element
MDIE – Mobility Domain information element
FTIE – Fast BSS transition information element

Authentication Sequence 2-

Re-association Request

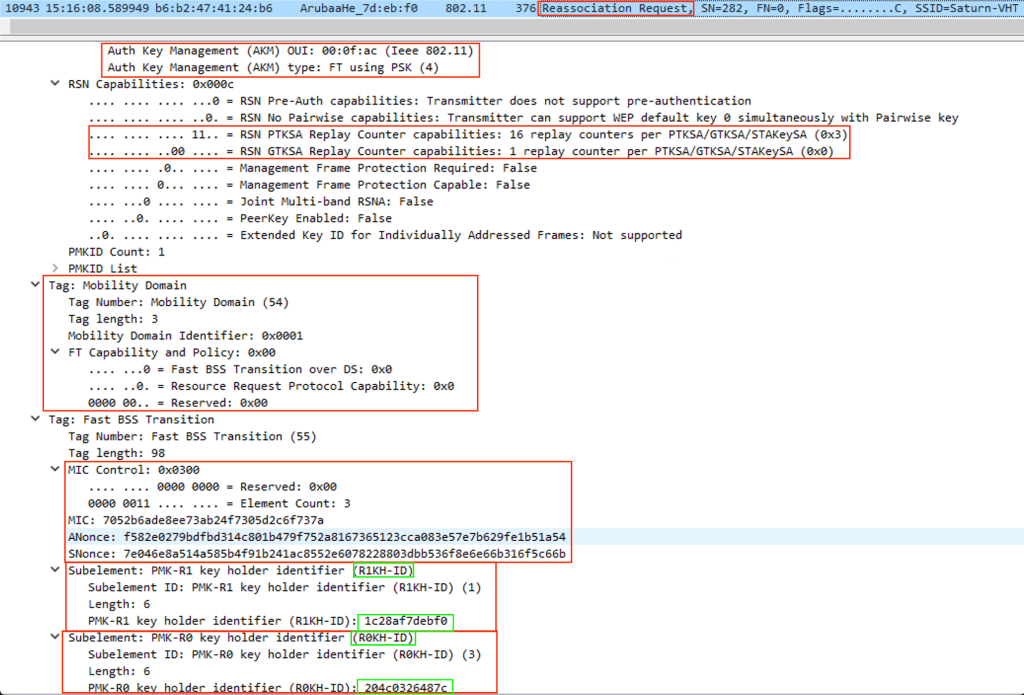
Re-association Response

Over-the-Air FT Mechanism
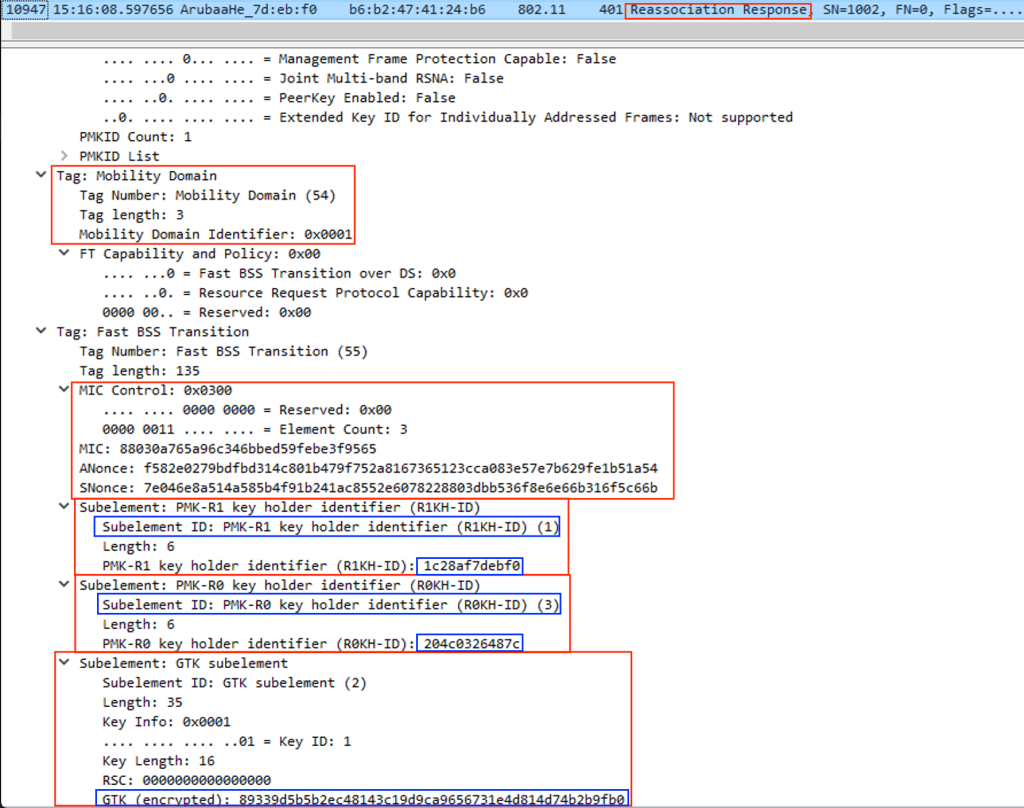
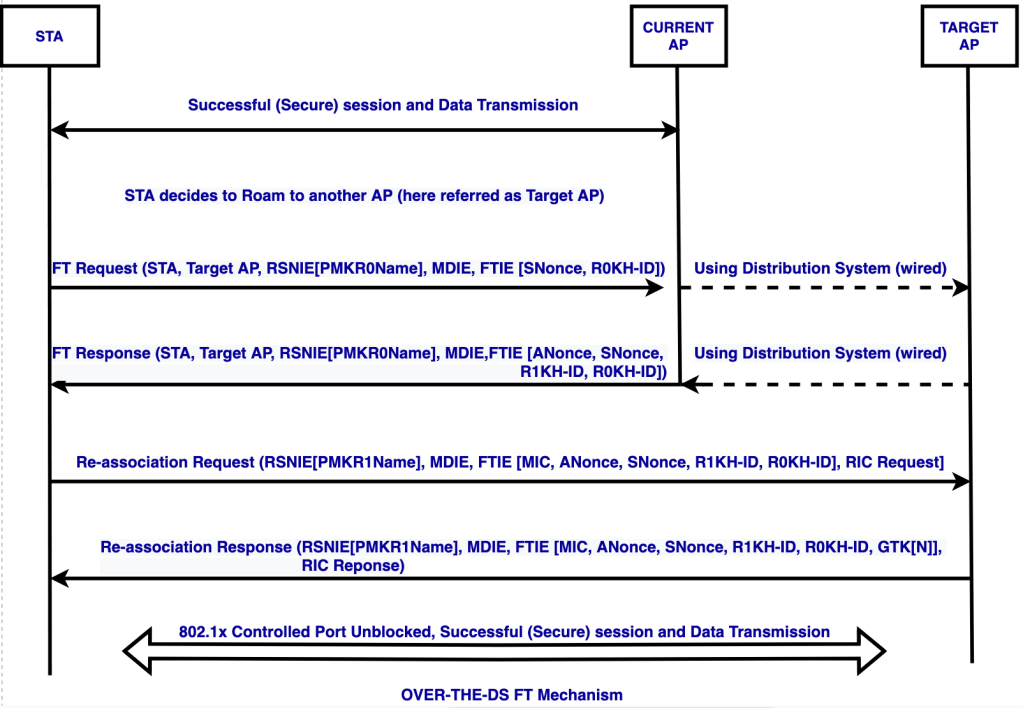
When using Over-The-DS FT mechanism, the client while deciding to roam to a new AP, will send FT Request frame to its current AP.
The Current AP then forwards that FT request frame to the Target AP using the wired infrastructure.
The target AP then replies back with FT Response frame to the Current AP so it can reach the client.
after receiving the FT response, the client then sends the Re-association frame directly to the Target AP and get a direct reply from the Target AP.
By the re-association response frame, both the client and the controller/AP will have PTK and GTK keys to protect the 802.11 data frames.
References :
CWSP Study Guide