Simultaneous Authentication of Equals (SAE) is a new Pre Shared Key (PSK) based authentication introduced in IEEE 802.11-2016 specification that intends to replace the less secure WPA2-PSK authentication.
Why SAE over PSK ?
With Pre Shared Key, the chances of offline dictionary attacks are more where an attack can be performed by obtaining a ciphertext generated using the password-derived key, and trying each password against the ciphertext. With this, it can runs through all possible passwords– up to 400,000 per second– to find right one.
SAE replaces PSK, as instead of using the PSK as the PMK, SAE derives PMK, by mapping the PSK to an element of a finite cyclic group, PassWord Element (PWE), doing FCG operations on it, and exchanging it with the peer.
WPA3-SAE
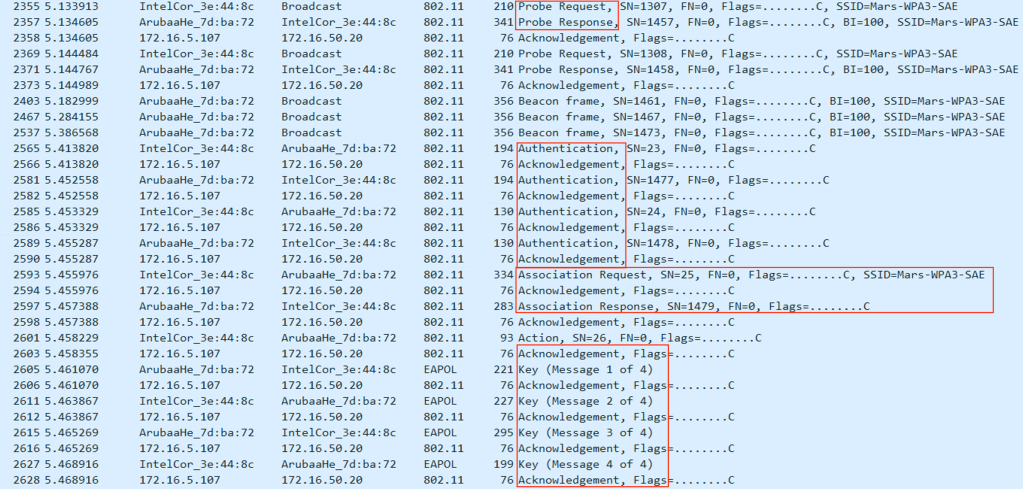
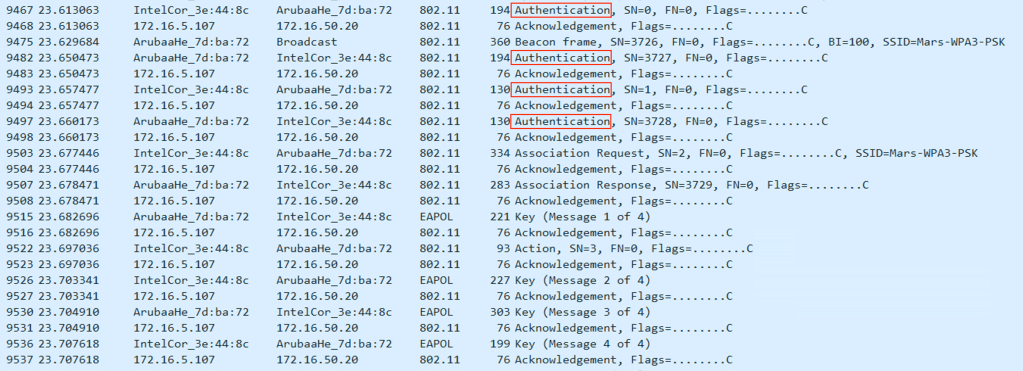
Below is the communication between the AP and WPA3-SAE client.
Note: If clients (like – older devices) which are not capable of supporting WPA3-SAE only mode , we’ll just see the connection failed or unable to connect error.
To add support for older clients which don’t support SAE, Beacons should broadcast WPA3-SAE capabilities in Transition Mode (discussed later in this blog).
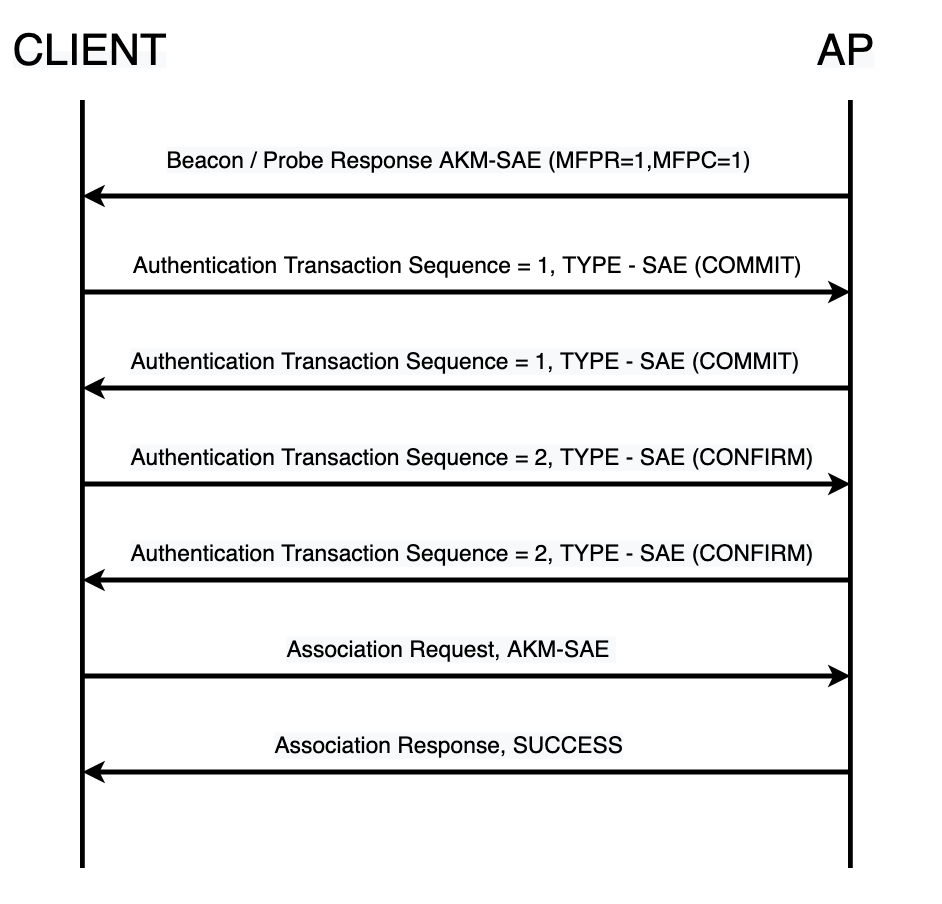
This is an overview of the management frame exchange seen during the WPA3-SAE transactions
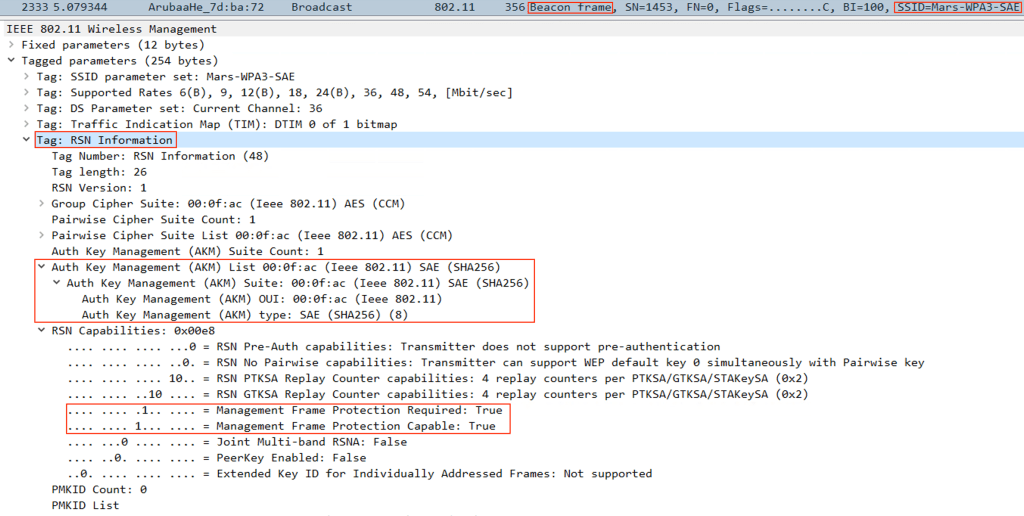
Beacon Frame:
The Access Points that supports SAE authentication key management, will specify its capabilities in the Beacon field
Aruba AP’s advertise support for SAE by using an AKM suite selector for SAE (00-0F-AC:8) in all beacons and probe response frames it issues.
When it is SAE only mode (no legacy PSK support), the MFPR and MFPC fields are set to 1.
Probe Request:
When the SAE capable client wants to connect, it sends a request to initiate the connection and will send out a broadcast probe request, which is heard by all the AP’s in the clients’ vicinity.
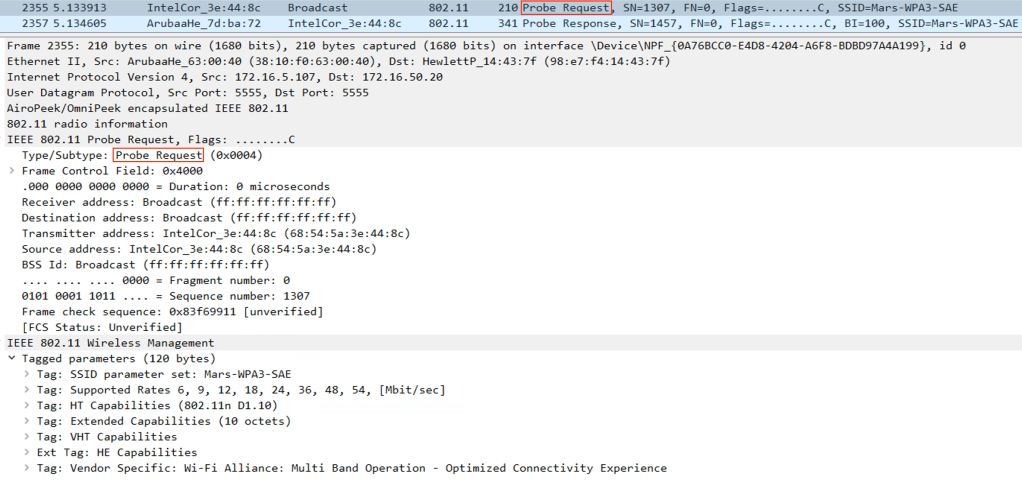
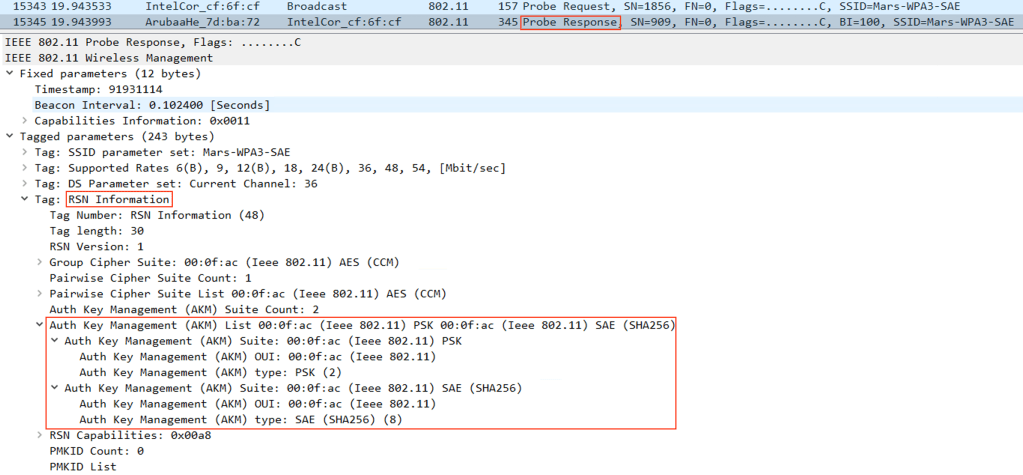
Probe Response:
Probe Responses by AP’s will mostly carry the same set of capability information that the Beacon indicates.
MFPR and MFPC is set to 1 here as well.

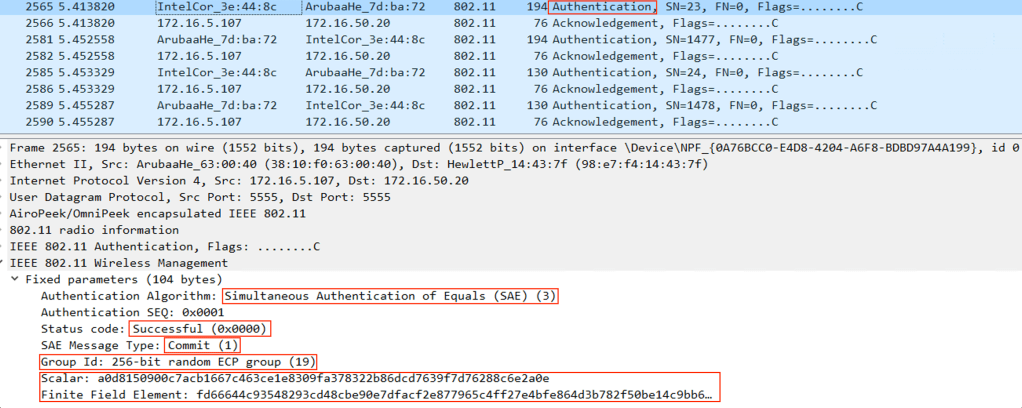
Authentication Transaction Sequence 1 – (COMMIT)
A client performing SAE sends an 802.11 authentication request with Authentication Algorithm set to ‘SAE’–Value 3 .This frame will contain a commit message i.e. “Authentication Transaction Sequence’ set to 1, an FCG, commit-scalar and commit-element
The value of Scalar is used to set a point in the elliptical curve which is represented as a Finite Field element. These (Scalar and Finite Field Element) are then later used to create a PMK. More information on Elliptical curve can be found here https://wirelessbuff.com/2021/07/21/details-on-cryptography/
AP and client both need each other’s Scalar and Finite Field values to generate PMK, and the first Auth Sequence carries these information on behalf of the client.
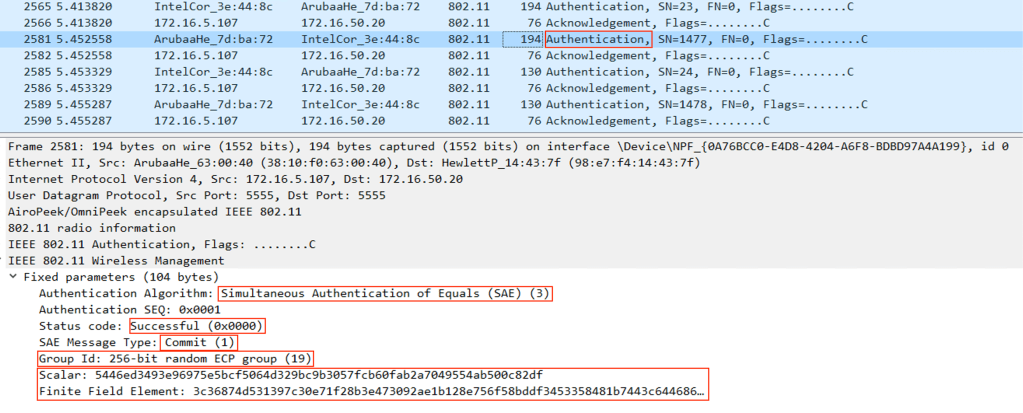
Authentication Transaction Sequence 1 – (COMMIT)
The AP then sends its own Authentication Commit frame and also specifying its Scalar and Finite Field value to the client which will be used in the PMK formation. and sends the same to the Client. Every other field remains the same.
Authentication Transaction Sequence’ for this COMMIT frame will be 1.
Authentication Transaction Sequence 2 – (CONFIRM)
At this point both the client and AP have the necessary data to derive PMK.
Now controller/AP and the client can compute the PMK, and send the confirm message to each other – using Authentication Frame with ‘Authentication Transaction Sequence’ set to 2.
This is Clients’ CONFIRM message (Send CONFIRM – 0)

Authentication Transaction Sequence 2 – (CONFIRM)
This is AP’ CONFIRM message (Send CONFIRM – 1)

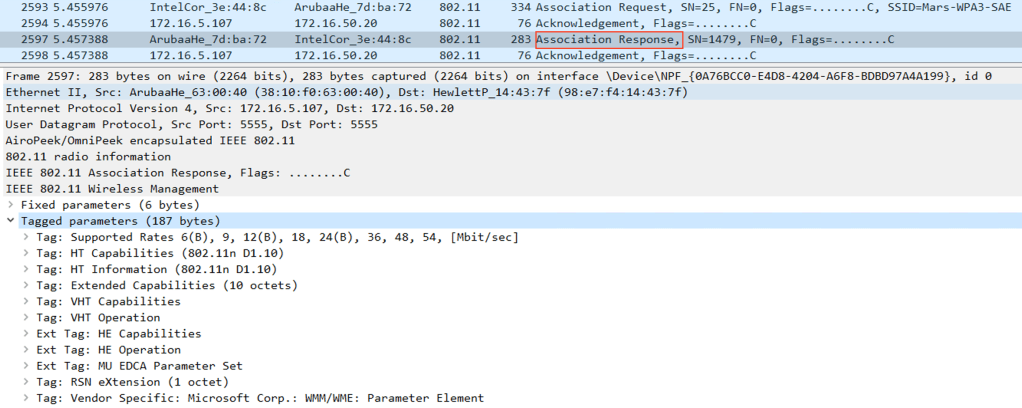
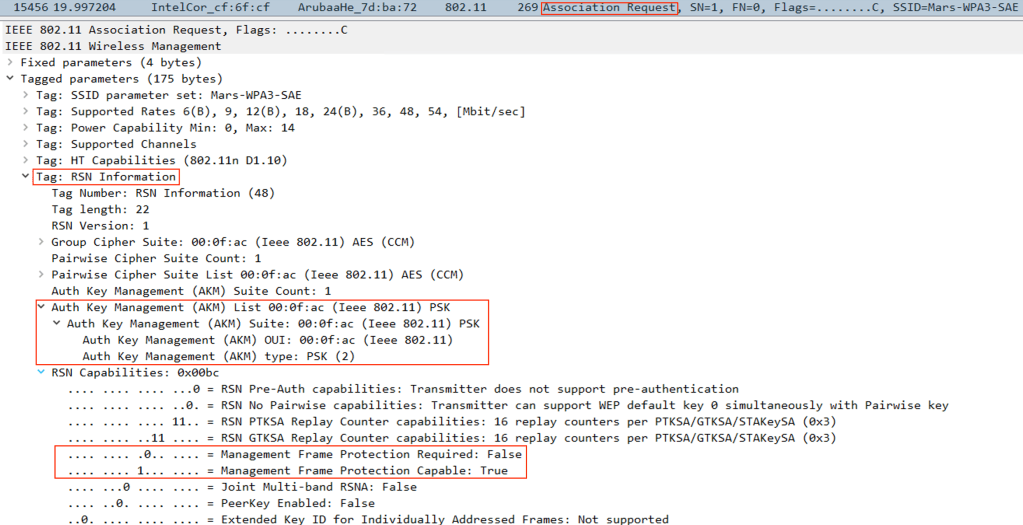
Association Request:
The client then sends an Association Request – with the AKM suite set to SAE.
SAE capable client will send this request setting MFPR and MFPC to 1.

Association Response:
AP then responds with Association Response
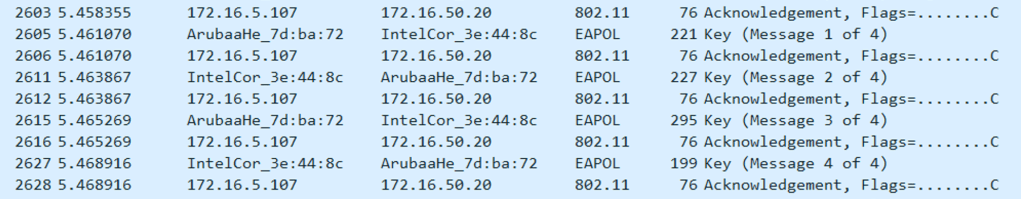
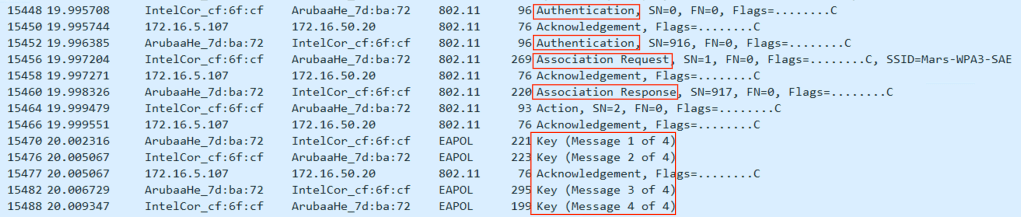
4-WAY Handshake:
AP then initiates a 4-way key handshake with the client to derive the PTK and GTK.
SSID information on Aruba Controller showing the encryption type as WPA3-SAE-AES.

WPA3-SAE transition mode
WPA3-SAE Transition Mode allows both SAE capable clients and clients that can only perform WPA2-PSK to be connected to the same BSS.
Beacon Frame
Access points sends out beacon or probe responses containing AKM list which will have both :
1. PSK (00-0F-AC:2)
2. SAE (00-0F-AC:8)
In order to support the non-SAE capable devices, the Management Frame Protection Required field is set to 0 and Management Frame Protection capable field is set to 1

When SAE Capable Clients connects in Transition Mode
When WPA3-SAE supporting client initiate a connection, this is how the Assoc Request looks like,
Then there will be 4 Authentication Transaction Sequence frame exchanges, as shown in above screenshots (as in WPA3-SAE only mode).
Association Request :
Since this client is capable of supporting SAE, it will choose SAE as the key management type and specify MFPR and MFPC fields as 1

When Non-SAE Capable Clients connects in Transition Mode
Clients which don’t support SAE, will use the legacy PSK based authentication.
So this time there will only be 2 Authentication frame exchanges as we would expect to see in PSK based authentication.
Probe Request:

Probe Response:
For the PSK based clients, there will be only 2 Authentication Sequences (unlike SAE connection which had 4 sequences)
Authentication Sequence 1
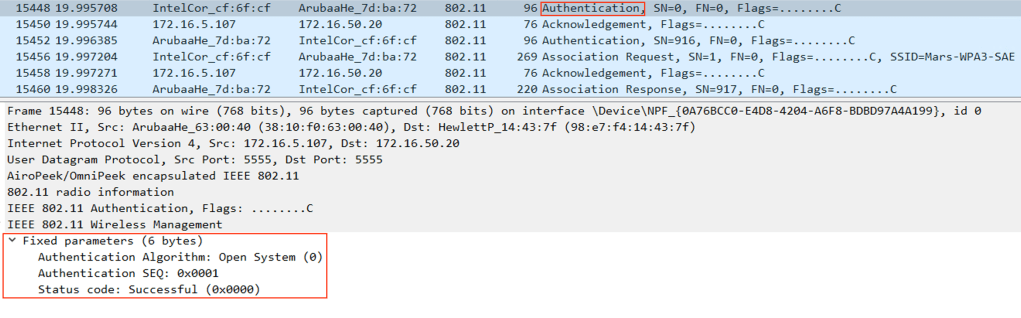
Authentication Sequence 2

Association Request:
Since this client is not capable of supporting SAE, it will choose PSK as the key management type and specify MFPR as 0 and MFPC fields as 1.
Association Response:

SSID information on Aruba Controller showing the encryption type as WPA3-SAE-AES and WPA3-PSK-AES, when Transition mode is enabled.

Off-loader statistics showing the total number of SAE Commit or Confirm requets nd responses from the Aruba Controller.
